In our last blog, we discussed the renewed emphasis on Zero Trust Security in the Biden Administration Executive Order on Cybersecurity. This comes on the heels of new zero trust guidance from the NSA and NIST, driven in large part by this year’s massive breaches, including SolarWinds, Microsoft Exchange, Colonial Pipeline, and many others.
The concept of zero trust is not new – it was made popular by Forrester analyst John Kindervag over a decade ago, and it makes logical sense to shift our security thinking and focus on solvable problems. The logic of zero trust is sound – don’t implicitly trust anything and verify everything. But in practice, zero trust has largely been thought of as an access control problem – making sure only the right users, and devices, can access the right corporate networks or applications.
However, attacks like SolarWinds have brought home a stark new reality – in many cases, the attackers are already inside your networks and have planted backdoors for repeated access. Just like the typical bank heist movies, the security guards have been easily fooled, while the thieves are breaking into the vault from underground. The flaw is not with the zero trust model – it’s that we’re not going deep enough or enforcing zero trust continuously across our networks and application stacks.
At Avocado Systems, we believe that zero trust is critical, but we must move beyond the hype, recognize the limitations of existing security tools, extend zero trust deeper, and automate it across enterprise applications. If we assume that attackers are already inside, then it’s critical to ensure that they can’t corrupt applications, can’t move laterally across systems, and that we can detect and stop these advanced attack techniques in real-time.
Moving to a Positive Security Model
Most of our current security technology revolves around the outdated concept of threat hunting. In theory, if we can identify specific malware, find the source, and react quickly, then we can prevent future damage from the “known bad.” But this has led to never-ending threat chasing, massive signature databases, and over-hyped use of AI/ML to try to solve this infinite problem. The reality is we’re not catching up – in fact, we’re falling further behind every day as attackers create infinite malware variants and use their own AI to mislead security systems. This negative security model of “chasing bad” is becoming increasingly ineffective and irrelevant.
Despite its negative name, zero trust actually represents a positive security model of “ensuring good.” Rather than endlessly chasing unknown threats, zero trust shifts our focus to what we can know – users, devices, networks, and applications – and only allowing what we explicitly know to be good and blocking everything else.
While you can’t argue with the logic of zero trust – don’t implicitly trust anything and verify everything, in practice, most zero trust initiatives in the last decade have proven impractical.
It’s Not Just About People & Devices
The first wave of zero trust solutions focused primarily on access control for remote users – who, what, where, and maybe when. While access controls remain important, it’s difficult to enforce granular controls for large organizations with thousands of users and devices, and hundreds of applications. Restrictive, least privilege policies usually get undermined by exceptions, which when granted, often get forgotten and ignored. In practice, many IT teams have found zero trust to be difficult to implement, and impossible to enforce over extended periods of time. Once again, these policies are generally enforced at the perimeter, and not continuously verified.
A larger challenge is that modern application workloads leverage complex, distributed stacks, connected APIs ecosystems, and automated traffic that traverses traditional network boundaries. As a result, a majority of today’s network traffic is intersystem or “east-west” communications. These data exchanges happen well after user-based perimeter Zero Trust controls end, essential leaving all zero trust controls at the proverbial front door.
Our mission at Avocado Systems is to apply zero trust inside the traditional perimeter, going deep into application workloads. The goal is to detect and block unauthorized and/or malicious activity traffic within your trusted environment, limiting the damage that Advanced Threats can do, even if they make it inside (and they always seem to find a way).
Zero Trust Must Go Deeper
Today’s Advanced Threats are consistently finding ways to go below the radar of conventional security tools, exploiting gaps and vulnerabilities in areas where we lack visibility. For example, firewalls, or WAFs at the network edge may stop some threats but lack visibility and control for threats already inside the perimeter. Similarly, network-level controls may detect unusual traffic patterns, but lack visibility into the content. Host-level controls, such as EDRs, have more proximity to servers, but lack depth visibility and cannot enforce zero trust principles for specific trusted processes (e.g. bash) and data exchanges.
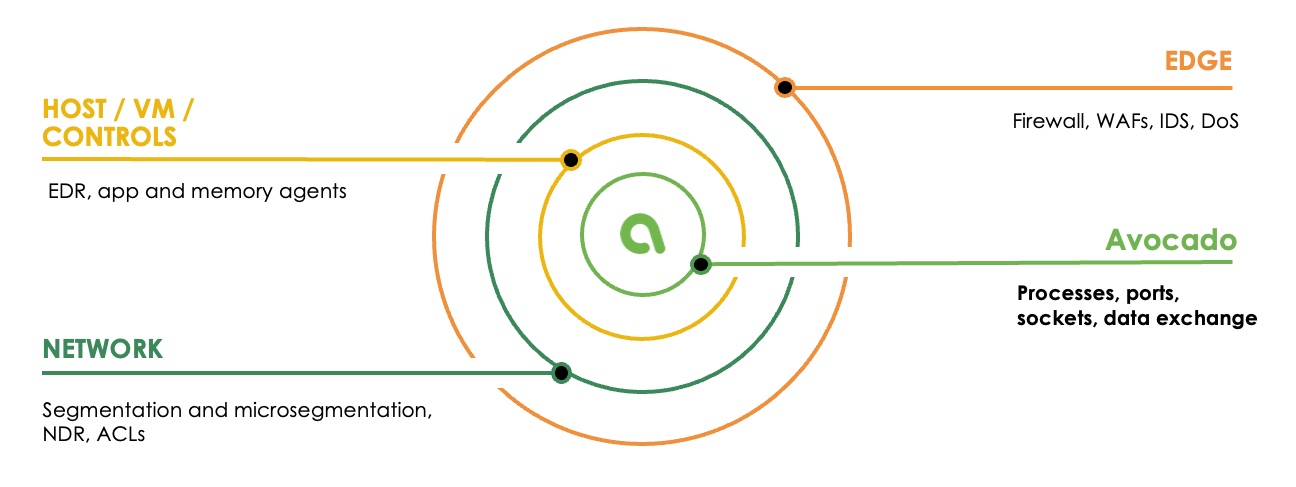
Avocado is unique in going deeper than existing security tools and enforcing zero trust security down to the application process level, protecting ports, sockets, data exchange, and lateral traffic between systems. This is critical in stopping Advanced Threats that operate beneath host-level security or exploit existing trusted applications and processes. If we can’t keep the bad guys out, we need to make sure we can catch them in the act before they can cause damage.
Applying Zero Trust Everywhere
Conventional zero trust security is flawed because it stops at user access to a protected resource. For example, you may continuously verify user access to an application, but there are no zero trust controls to continuously verify the application’s interactions with other trusted systems within the workload environment. The reality is that attackers continuously find ways in and will exploit trusted systems to spread and wreak havoc. As we saw with the Microsoft Exchange attacks, static security was helpless against new vulnerabilities that were not known in advance to existing security tools.
At Avocado Systems, we focus on stopping the effects of Advanced Threats, regardless of the specific vulnerabilities or attack techniques – zero day or otherwise. By enforcing zero trust at the application process level, we can detect illicit activity or lateral movement caused by attacks, and instantly stop it in its tracks, stopping attackers “in the act” and preventing damage. This is not a one-time process, as we protect critical applications throughout their entire runtime lifecycle.
The solution enforces zero trust continuously during runtime and ensures that only explicitly authorized lateral traffic is allowed, blocking all rogue connections and movement by the bad guys. Avocado detects and stops advanced threats that were previously undetectable, and protects applications with advanced security against tomorrow’s unknown attacks.

